Understanding the complexity of personal crimes is crucial in today’s world where privacy is often under threat and personal boundaries are frequently crossed. This guide aims to equip you with the knowledge and tools needed to identify, address, and prevent personal crimes, ensuring your safety and well-being.
Every day, individuals encounter situations where personal boundaries are violated, and understanding what constitutes a personal crime is vital. From privacy invasions to harassment, knowing the nuances of these crimes can help you recognize them early and take necessary actions to protect yourself.
Why Understanding Personal Crimes Matters
Recognizing personal crimes is a fundamental step towards safeguarding your rights and personal space. The impact of such violations can be profound, often leading to emotional distress, loss of privacy, and even physical harm. Understanding these crimes helps you take proactive steps to prevent them and respond effectively if they occur.
Imagine walking down a street only to find your personal information being shared in a public forum. Or someone consistently disregarding your physical space, making you uncomfortable. These scenarios are not just annoying; they can be serious breaches of your personal rights.
Quick Reference
Quick Reference
- Immediate action item with clear benefit: Always keep personal information private and be mindful of how and where you share it.
- Essential tip with step-by-step guidance: Create strong passwords and enable two-factor authentication on your accounts to safeguard your digital privacy.
- Common mistake to avoid with solution: Avoid oversharing on social media. Limit what you post to protect your personal boundaries.
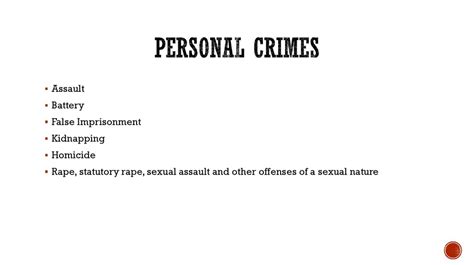
Identifying Personal Crimes: A Detailed Exploration
Identifying personal crimes starts with understanding the various forms they can take. Below we’ll explore the different types of personal crimes and how to recognize them.
Privacy Invasions
Privacy invasions occur when someone violates another’s personal space without consent. This can include unauthorized surveillance, hacking into personal accounts, or publicly sharing private information.
For example, if someone uses your email or social media accounts without permission, this is a clear invasion of your privacy.
How to Recognize Privacy Invasions
Recognizing a privacy invasion often involves feeling uncomfortable or being aware of unauthorized access or use of your personal information. Signs may include:
- Unexpected account logins or changes.
- Strange messages or emails sent from your accounts.
- Your personal information being publicly shared without your consent.
When you notice any of these signs, it’s crucial to take immediate action to protect your information.
Steps to Address Privacy Invasions
If you suspect a privacy invasion, follow these steps:
- Change your passwords: Use strong, unique passwords for all your accounts and enable two-factor authentication where possible.
- Monitor your accounts: Regularly check your bank statements, emails, and social media for any unauthorized activity.
- Report to authorities: If the invasion involves hacking or other criminal activities, report it to the appropriate authorities, such as local law enforcement or cybersecurity agencies.
Harassment and Cyberbullying
Harassment involves repeated unwanted actions that are intended to upset, alarm, or coerce someone. Cyberbullying is a type of harassment carried out through digital platforms.
How to Recognize Harassment and Cyberbullying
Harassment and cyberbullying can be identified through persistent unwanted messages, threats, or public humiliations.
- Unwanted messages or comments, including hate speech.
- Threats or intimidation through any communication channel.
- Doxxing or the public release of private information.
Steps to Address Harassment and Cyberbullying
To address harassment and cyberbullying, consider these actions:
- Block and report: Block the harasser and report the behavior to the platform’s support team.
- Document everything: Keep records of all communications and instances of harassment.
- Seek support: Talk to friends, family, or professionals about what you’re experiencing for emotional support.
- Legal action: If the harassment is severe, consult with a legal expert to understand your rights and potential legal actions.
Physical Assault and Unauthorized Contact
Physical assault and unauthorized contact involve direct physical harm or unwelcome physical contact. These acts can be intimidating and dangerous, requiring immediate and decisive action.
How to Recognize Physical Assault and Unauthorized Contact
Signs include physical injuries, unwanted physical touch, or someone following you persistently.
Steps to Address Physical Assault and Unauthorized Contact
- Safety first: Ensure your immediate safety by removing yourself from the situation.
- Document the incident: Note the details of the incident, including time, location, and any witnesses. If in immediate danger: Call emergency services right away.
- Report to authorities: File a formal report with local law enforcement.
- Protective measures: Consider self-defense classes or obtaining a restraining order if necessary.
Practical FAQ
What should I do if I realize my personal information has been stolen?
Immediate steps to take include:
- Changing passwords on all accounts where your information was used.
- Monitoring bank and credit card statements for any unauthorized transactions.
- Contacting your bank and credit card companies to report fraud and freezing accounts if necessary.
- Filing a report with your local law enforcement agency.
- Checking your credit report for any suspicious activity and placing a fraud alert if needed.
Taking these actions quickly can help minimize damage and protect your financial well-being.
How can I prevent my personal information from being shared online without my consent?
To prevent unauthorized sharing of your personal information online, consider these measures:
- Restrict your privacy settings on social media platforms.
- Think twice before sharing personal details like home addresses, phone numbers, and financial information.
- Regularly check for privacy settings and adjust them to limit who can see your information.
- Use strong, unique passwords and enable two-factor authentication for your accounts.
By being cautious and proactive about your digital presence, you can significantly reduce the risk of your information being shared without your consent.
Understanding personal crimes and knowing how to address them is essential for maintaining your personal integrity and safety. By recognizing the signs and taking proactive steps, you can protect yourself and ensure that your rights and privacy are respected.